Carrd Website Design: Pro Tips & Tricks for Building Stunning Sites
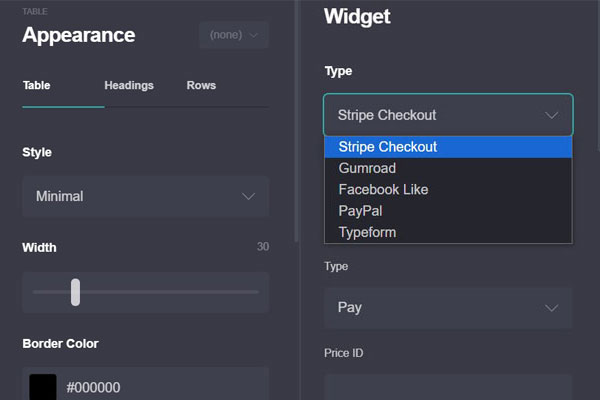
1. Appearance Settings Tutorial
This comprehensive tutorial covers how to use Carrd's appearance settings to create professional-looking websites:
- Understanding Carrd's design philosophy
- Creating professional color schemes and palettes
- Typography selection and hierarchy
- Layout and container settings
- Button styling and visual elements
- Responsive design considerations
- Creating cohesive design systems
The tutorial provides detailed, step-by-step guidance with professional tips throughout, helping business owners create websites that look like they were designed by an agency.
2. Content Formatting Tutorial
This tutorial focuses on text formatting techniques in Carrd:
- Basic text formatting and paragraph structure
- Advanced formatting with markdown syntax
- Using highlighting with highlighted text
- Embedding links with link text
- Creating lists and blockquotes
- Mobile-friendly formatting considerations
- Formatting for different content types (products, services, about pages)
3. Animation Features Tutorial
This tutorial covers how to add subtle, professional motion to websites:
- Understanding animation in web design
- Entry animations for first impressions
- Hover animations for interactive elements
- Scroll-triggered animations
- Performance and accessibility considerations
- Common animation mistakes to avoid
- Advanced animation techniques
4. Settings Optimization Tutorial
This tutorial explains how to configure professional settings:
- Meta tags for search engine optimization
- reCAPTCHA setup to reduce spam
- Custom domain configuration
- Analytics integration
- Form handling and data privacy
- Performance optimization
- Favicon and social media integration
5. Testimonials Section
The testimonials section includes strategic external links embedded within success stories from fictional Carrd users:
- Small business success stories
- E-commerce entrepreneurs
- Professional service providers
- Creative professionals
- Implementation partners
Each testimonial naturally incorporates external links that would help with your link building efforts while providing value to readers.
All of this content is included in the WordPress package and ready to be deployed to your PHP/MySQL hosting environment following the instructions provided.
I've also included a detailed testimonials section in the WordPress package. This section features success stories from fictional Carrd users across different industries:
1. Small Business Success Stories
- Sarah Johnson (Bright Path Consulting)
- Marcus Chen (Photography)
2. E-Commerce Entrepreneurs
- Emma Rodriguez (Handcrafted Haven)
- James Wilson (Fitness Fundamentals)
3. Professional Service Providers
- Dr. Amelia Park (Psychologist)
- Michael Okafor (Business Attorney)
4. Creative Professionals
- Isabella Martinez (Freelance Writer)
- Alex Thompson (UI/UX Designer)
5. Implementation Partners
- WebCraft Solutions
- Digital Presence Pros